
SWOVUG Q2 2017 - Nimble Storage
This past Thursday (April 20th, 2017) was the first SouthWest Ontario Veeam User Group (SWOVUG) meeting of the year. Considering the weather, attendance was pretty good and with that, we had some lively conversations and presentations, which is the whole point of a user group. There were lots of new faces, and many familiar ones, which is always a great mix.
This meeting also marked the group’s beginning of its second year. The inaugural meeting was held in March 2016, and the group itself was technically brought into existence in December 2015. Happy 1st Birthrday SWOVUG!
After I performed my introductions and highlighted the agenda, we jumped right into our sponsored session with Nimble Storage. Nimble Storage is one of a handful of storage companies who I would consider the ’new breed’. These are companies that have looked at traditional storage, figured out what works, but more importantly what was missing and went to market with it. In this session, we received a fairly deep dive into the product, and we touched on how it has a tight integration with Veeam, particularly with the snapshot integration introduced in Veeam Backup & Recovery version 9.5.
The session itself went longer than planned, but part of the reason why I let it go that long is because we were seeing a lot of great questions thrown at the presenter. Kudos to Domenic from Nimble Storage for taking all the questions, and sticking it out.
VEEAM SERVER EST PRACTICES
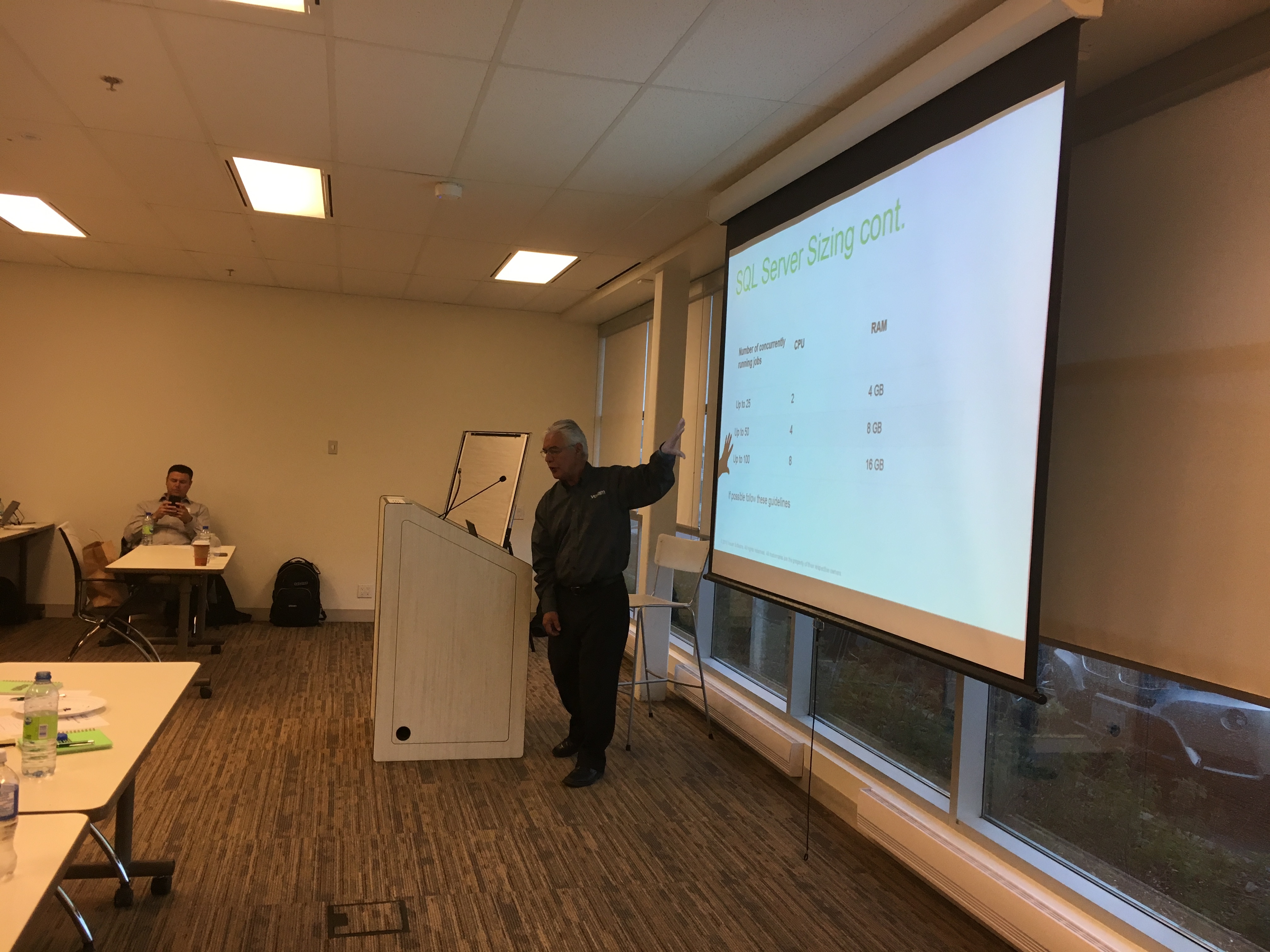
After lunch, myself and Mario Marquez presented on Veeam Server Best Practices. We knew this we going to be a big topic, and our suspicions were confirmed when we ended up going for about 90 minutes, only ending due to the fact that our event was ending. Mario mentioned that the slide deck would be mailed out, however, I also have a copy available for download.
SWOVUG Q2 2017
We had a few great questions along the way that I want to circle back to. One was regarding the recommended RAID configuration for disks. I wanted to drill down into that a bit as some great points were brought up. During the presentation, RAID 6 was mentioned as recommended - this would allow for two disk failures and still allow access to your data. A very good point was brought up that RAID 10 should be recommended (mirrored and striped) as this would give you lots of protection, and would see great performance - the best of both worlds! It is definitely hard to argue against RAID 10, other than to say that the cost to implement it is quite high when compared to the other options. With RAID 10 you immediately loose half of your capacity due to mirroring, which means you’ll need twice as much storage. There was a great discussion on this which basically boiled down to if you can get funding for RAID 10, then jump on it. Otherwise, make sure to choose RAID 6 over RAID 5 (single disk loss).
Another discussion point revolved around ransomware going out and specifically deleting your backup files. Veeam is by no means more vulnerable than when compared to other solutions, it all comes down to designing the solution properly. If you are using a Windows Server as a backup repository, make sure you do not have file sharing enabled - there is no need to access the backup files via a Windows share. If you are using some sort of SMB (CIFS) share, then make sure that the repository is not on the domain. You can setup a local account on the repository and then store those credentials in the Veeam job - that way the only access to the repository is via the Veeam job.
Lastly, the question of Cloud Connect being secure as an offsite location came up. The answer is ‘it depends’. Yes, there will be an air gap between your local network and the Cloud Connect repository, so malicious code such as Cryptolocker won’t be able to hit your backups. However, if you have a malicious admin or a compromised password, then an attacker could still log onto the Veeam Backup & Recovery server and do ‘bad things’ from there.
The long and short of it is that you need to practice defense in depth. Make sure you have multiple layers of security and multiple copies of your data. If you have a tape backup sitting in secured storage, not connected to anything, then it will be safe from Cyrptolocker at the time of the attack. Just be sure that when you do bring it online that you are in a ‘clean’ environment as you wouldn’t want your backup to be encrypted at that point.
NEXT SWOVUG
As of right now, we do not have a date lined up for the next SWOVUG meeting. We are toying with the idea of doing a full day event later this year (potentially in October). So if that is something that is of interest, or if you have any other feedback or thoughts, feel free to reach out via email, Twitter, or leave a comment below. There is an upcoming ‘Virtual VUG’ slated for Tuesday, June 13th. It will be hosted by Rick Vanover and I will have a speaking slot. Keep an eye on https://go.veeam.com/user-groups for details.
